

Osu!
30/9/2017
Following my departure of playing CS:GO and most of its communities I needed something new to fill my spare time, of which I have a lot of. For a while now I've been watching gameplay of osu, considering its target audience, it was only a natural transition.
I began playing opsu, an open source osu client written in Java. Opsu is a great alternative to the (currently) Windows only osu, however, I eventually wanted to experience the real deal.
Following a fantastic tutorial for installing osu on Linux via WINE by Francesco149 I was able to experince the real deal. Comparing opsu to osu is unfair, however differences are very apparent, the most obvious for me was input lag found in opsu. However, I didn't notice it until I tried osu.
After a few months of using a mouse I ended up purchasing a tablet, specifically the HUION H420. The tablet is incredibly cheap and works amazingly. It took a few weeks to get up to speed with speed and accuracy compared to what I could do with a mouse, and I am now vastly better than I ever was. I had real difficulty learning how to hold and use the pen however, mainly because I write with my left hand and control the mouse with my right. My right hand has never written before and didn't understand how to use a pen. I deemed learning how to control the pen in my right hand easier than using the other with a pen due to my left hand knowing how to repeatedly press button with speed and accuracy over years of gaming.
I still suck at the game however, but it's mighty fun.
Osu! profile
As a passing tip, put a little piece of velcro on both the side your monitor and the upper part of your pen, it's a great convenient place to store it when not in use.


Starting afresh
3/9/2017
Yesterday upon restarting this server everything went to hell. OOM killer began killing processes regardless of the >1gb ram available and no in-bound or out-bound connections were working. I don't know at what point I screwed things up and the uptime on the system was >200 days. Instead of hunting down the problem, I decided reinstalling the operating system was the best choice.
I spent the entirety of yesterday setting up my email server, IRC, ZNC etc and only today am getting around to doing the small things.
This is the first time I've ever needed a backup, and thankfullt my prior preperations for a disaster scenario paid off.
Things lost
a few hours of email
a few hours of IRC logs
months of Slack logs
Argh, the Slack logs, this annoys me the most - seeing as it was a somewhat recent addition to my backup routine I hadn't put them in a directory that is included in my system backup (I don't let the backup script backup the backups, recursion to the Nth degree) and this is where I stored my MongoDB dumps. I feel like an idiot, but, in the scheme of things this is a very minor loss. I manged to get my entire email collection and IRC log restored, I am very glad about that.
This was an amazing learning experience and allowed me to test my backup system in a realistic scenario, and all things considered, it worked really well. Now to improve it.
I do have the raw /data/db MongoDB directory however, if I can learn how to restore it from these files, I will be a happy man.
Later edit: Well, i'm dumb, the mongo databases were never located in /data/db, so I considered them lost. Today I thought that maybe my default db location was different, and indeed it was. So now I have everything and have put my logging script back on hourly. I lost an entire month of logs, but oh well.

New static website
27/8/2017
My previous website relied heavily on php/databases to deliver content, it was slow and did not render correctly inside my terminal web browser.
For these reasons I created my own static website generator using Python. The script is configurable using a cfg file.
You can find the project on Github


Game of Life in C and ncurses
17/8/2017
Wanting something to do today I created a clone of Conway's Game of Life in C using ncurses. The project can be found on GitHub.

Binary
6/8/2017
Surprisingly i've never looked at learning how to count in binary, so, the other night I did.
Binary is a base 2 counting system, meaning you have 2 numbers available, 0 and 1. Most humans use base 10 (give this some research, interesting stuff), the numbers 0 through to 9 and considering we've grown up with thsi technique, it's easy to us. I was surprised at how simple it is to count in binary utilising your own base 10 knowledge.
For this post we're going to be using 8 bits (which equates to one byte, better known as a single character like 't'). A bit is a single 0 or 1, so 8 bits equates to something like this '0 0 1 0 1 1 0 0' which is the number 44.
But, how do those seemingly random 0's and 1's equal 44? This is where things get fun.
each of those bits (8 either 0's or 1's) equates to a number, this number is doubled for every bit, for example, using 4 bits the value increases like '1, 2, 4, 8). However, in binary these numbers are REVERSED '8, 4, 2, 1', the most significant number on the left.
Let's set our our 8 bits in order to equate 44:
128 64 32 16 8 4 2 1
Now, let's place our 0's and 1's in their correct position:
| 128 |
64 | 32 | 16 | 8 | 4 | 2 | 1 |
|---|---|---|---|---|---|---|---|
| 0 | 0 | 1 | 0 | 1 | 1 | 0 | 0 |
32 + 8 + 4 = 44. This is the binary representation of 44.
With these 8 bits we can count from 0 to 255 (entire ASCII table), awesome.
So with this knowledge and a little practice you can begin to count using binary pretty easily. But, now you want to spell out words, well, you can do that too.
ASCII is a character encoding standard that is utilised in computers to convert decimals (previously binary) into characters us humans can understand. Using an ASCII table we can do this conversion ourself manually.
Lets utilise the lowercase english alphabet, as shown in the ASCII table the lower case 'a' is represented by the number 97 and the lowercase 'z' being 122, filling in the gaps we have the entire alphabet. Take note that the uppercase alphabet is represented from 65 to 90. Knowing this, writing out our name for example using binary is extremely easy, however quite time consuming. Let's do my name, 'daniel'.
01100100 = 100 = d
01100001 = 97 = a
01101110 = 110 = n
01101001 = 105 = i
01100101 = 101 = e
01101100 = 108 = l
Let's plug these numbers into an online binary to text converter such as this free website and input the string "01100100 01100001 01101110 01101001 01100101 01101100". Pretty simple in the end.
You can also utilise a neat trick designed to allow converting binary to text quickly. Take the last 5 bits of data ignoring the first 3, for example '01100' from the character 'l' above. Add the rows with 1's together, in this case 8 and 4 which equals 12. Now what is the 12th letter of the alphabet? That's right, 'l'. This trick works for both upper and lowercase characters, the difference being the first 3 bits of a lowercase character are 011, while for uppercase characters it is 010.
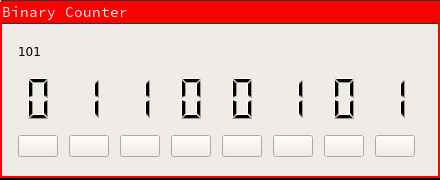
I created an 8-bit binary counter using Qt and C++ in order to practice my counting, it provides a real-time calculation of your number. You can find the source code here.

I'm bored and sick of CS:GO
30/6/2017
I'm an open book, the past is the past, mistakes are mistakes. My email is always open.
I'm not happy with life, I haven't been in a long time - I don't think this is much of a secret, if you knew me to any extent you would surely know. For the last 3 or so years my life has consisted of nothing other than playing Counter Strike and moderating the r/globaloffensive community (although that part has only been a thing for 8 or 9 months at this point). Thrown in I have also been trying to complete my final year of high school - 3 years, I still have not finished.
I can't go on like this, currently I have no plans, I have no dream, I have no future. I need something to change and I need it now.
The day before last I left the r/globaloffensive Discord and IRC channel, I have no interest in furthering myself with those two hangouts. I'm currently planning on leaving the r/globaloffensive mod team entirely sometime after the current trial period, possibly.
I have also decided to no longer play Counter Strike. my valuable skins have been moved to their original home (given to me by the one person I ever actually had fun playing with) and I only intend to play once weekly to complete the current operation.
All this isn't without reason. I am going to begin furthering my education by both attending and completing school and focussing on developing my programming knowledge. I have also began work on a portfolio showcasing a number of my projects.
After 2.2 thousand hours in Counter Strike Global Offensive I think I have well and truly had my $15 of enjoyment.
This is hopefully a turning point in my life - i pray that it is otherwise the alternative is ugly.
I didn't say goodbye to anyone in either of the communities I left, if you cared about my presence and am wondering why I left, i'm sorry.

RGB controller web page
4/6/2017
I've now integrated a server into my RGB controller that allows outside applications to send commands over a socket. The first project using this feature is an HTML/JS web page that uses PHP to send the commands. I have these running on a local server running a LAMP stack.
This addition broadens the future of this application and the things I can one day do.


RGB Controller improvements
21/5/2017
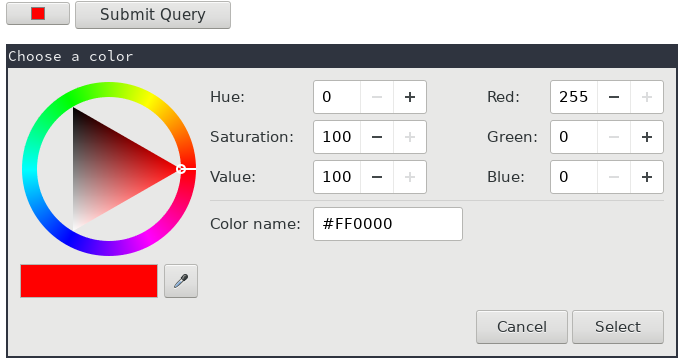
Recently I decided to overhaul my RGB Controller's interface. Originally, the interface was extremely tall consisting of all its features one upon the other. Now, I have used tabs allowing each function to have it's own section.
Along with the new interface I have added a new system that allows the host computer to check its connection status with the microcontroller, after 3 failed ping/pong attempts the program determines the connection has been lost and returns te program into it's default, non connect state. This feature has brought with it true two-way communication between the host and microcontrollrer, previously the communication was only one way, host -> microcontroller.
I have also integrated an IRC bot into the program, supplying it with a server, port, channel name and username you are able to take advantage of the full feature set of the GUI application using simple commands, "!send red=255" will for example set red to 255. These commands can be delimited by ';', for example "!send red=255;blue=255". The bot only takes commands from a hard coded user, this is easy to change and I plan to add an option in the UI to alter this.
Example of the current interface on the 'Fade' tab.


CS:GO bomb drop bind and how I overcame its one downside
2/5/2017
recently I was shown a bind for CS:GO that automatically switches to your bomb and drops it. This is great, however it has one problem: if you aren't in possesion of the bomb it throws your current weapon.
Of course, me being myself this was unacceptable, I had played a few games of matchmaking with this bind and I had dropped my gun by accident too many times (I bound it to mouse3, I also press mouse3 in game sometimes). The bind in question is bind mouse3 "use weapon_c4;drop".
Using Qt/C++ I created a console application that uses CSGO's game state integration to read current information form the game client. I have used this (and most of the code, too) in my CSGO stats application which had a feature rich game display using game state integration.
The application is simple, when the game detects you're currently in possesion of the bomb it writes the drop bomb bind to a cfg file, when it detects you don't have the bomb, it instead does nothing, in the case of this video it prints "I don't have the bomb". The cfg file is only written if the state changes, it isn't constantly writing to the file, that would be grossly inefficient.
example video

In need of a notification program, so I created my own
28/4/2017
While uploading an image to my file hosting service using the api and a script utilising curl, scrot and xclip I was left pasting the contents of my clipboard into the url bar hoping that, eventually the image url would be there. The script I was using had no way of reporting that it had finished, so I had no clue when it was. To solve this first world problem I needed a notification program. While installing one and configuring it would have been the easiest option, I instead decided to create my own. Using, like all my other projects, Qt and C++ I did just that.
The application is incredibly simple, however is very effective. The following command is what was used to create the notification seen in the image:
notifier "<b><u>Screenshot</u></b>" "<font color=green>uploaded and copied to clipboard.</font>" 5000
HTML tags are supported, allowing you to customise the text completely, you can also embed images. The top right includes a close button for easy removal and the application allows input of how long it should stay open until it closes itself, this is measured in ms. The notification appears correctly in the bottom right of my main monitor and has a customisable x and y offset. It resizes itself dynamically to keep all the content on screen.

The project is not as of yet on GitHub, i'm not happy with the quality of the code yet.


